Pirates of Somalia (35 page)
Read Pirates of Somalia Online
Authors: Jay Bahadur
Tags: #Travel, #Africa, #North, #History, #Military, #Naval, #Political Science, #Security (National & International)

* * *
At a chaotic guardhouse at Bossaso airstrip, scurrying travellers clamoured for boarding passes from a few overburdened officials. Upon handing over my passport I learned that, on my way into Somalia, the customs agent had scribbled the incorrect exit date on my visa stamp. Now, an official informed me that I had been in the country illegally for the past ten days and would be required to pay a fine of $200. I had spent the last of my US dollars on the wages of my bodyguards, Said and Abdirashid, and had no money for my exit ransom. Colonel Omar was stuck with the bill; he fixed me with one of his menacing glances, as if deciding whether he should arrest me, let me go, or shoot me. Beyond the chain-link fence separating the parking lot from the sand-covered airstrip, a mob was pressing around the gangway; the plane was starting to board. I left the Colonel grumbling at me and shouting at the official, and made my way onto the runway, past a solitary guard who made no motion to check my passport.
The Ilyushin Il-18 turboprop was Soviet-made, the seat fabric torn and seatbelts broken, but it was larger and seemingly sturdier than the rattletrap Antonov that had brought me into Somalia. I left Puntland decidedly less apprehensive than I had first arrived.
For me, Somalia will always be a land of adventure, my memories of it forged in a mixture of adrenaline and wonder. In the span of a few weeks, I had gone from writing marketing reports to tracking down pirates in one of the world’s most dangerous countries, under the protection of a man I had never before met. The romanticism of the journey was intoxicating.
Like their seventeenth-century forebears, the Somali pirates were outnumbered and outgunned, yet dared to challenge the might of the world’s navies, casting themselves as heroic defenders of their seas against the forces of foreign exploitation. It was hard not to feel some slight admiration for their reckless courage, regardless of the iniquity of its ends. In reality, the pirates more resembled self-interested, amoral, and often barbaric gangsters than principled crusaders, as any hostage seafarer could attest to. “It is when the pirates count their booty,” author William Bolitho once wrote, “that they become mere thieves.”
6
As the plane gained altitude, Bossaso shrank to a pale yellow smudge in the side window. A pair of Australian cameramen chatted loudly in the seats in front of me. Far below, the Gulf of Aden stretched to the horizon, blue and unbroken.
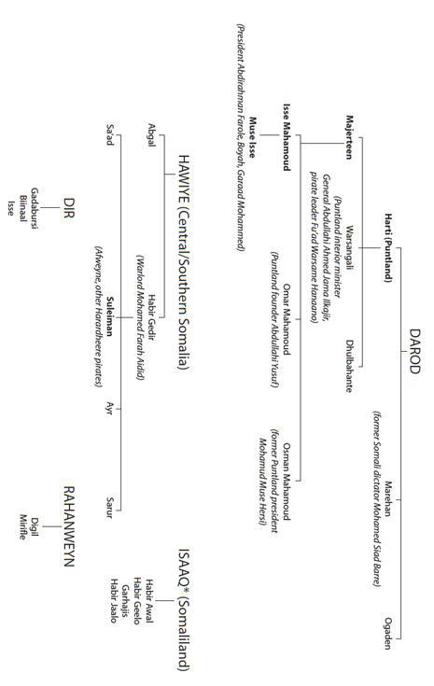
Appendix 1
Simplified Somali Clan Tree
*Considered by some to be a sub-group of the Dir.
Appendix 2
The
Victoria
Gang
I
N
C
HAPTER 14
,
WE LOOKED AT THE FEATURES OF THE
V
ICTORIA
that made her a tempting target. But what of her captors? How did Computer’s organization measure up to a typical pirate gang? Stig Jarle Hansen’s extensive research into the organization and operational methods of pirate groups allows us to establish a comparative framework with which to place the
Victoria
gang in perspective.
1
I will examine seven criteria in turn:
- Size
- Investment structure
- Cost structure
- Attack strategy
- Technology
- Role of the diaspora
- Other
1. SIZE
According to Hansen, “an average group tends to consist of around 12 to 35 individuals.” At 35 members, Computer’s organization was large, though still smaller than the top-tier operations, such as the hundreds-strong consortium of gangs involved in the
Faina
hijacking.
2. INVESTMENT STRUCTURE
Venture Capital
Hansen describes three methods of capital financing for pirate operations, which I label the “single investor,” “co-operative,” and “private equity” investment models. Under the single investor model, one man—often a local businessman—funds the entire operation, from the boats to the guns and the communication equipment. The cooperative, on the other hand, involves a number of equal shareholders joining together, each bringing his own guns and food (though the boat is owned by a specific member of the group). Finally, the private equity model consists of an individual who first raises capital from a number of willing investors, then proceeds to organize and direct the mission (like Afweyne, in the early days).
The
Victoria
gang operated under the single investor model, with Computer supplying the entire start-up capital and hence claiming a large slice of the company’s revenues. “In Puntland,” Hansen writes, “local researchers have identified 51 investors, mid-level businessmen mostly from the clans of the respective pirate group.” Computer’s name is probably on that list—particularly if, as suggested in
Chapter 14
, he is a known Puntland government fugitive.
Payroll
The majority of pirate gangs work on straight commission, a system Hansen playfully labels “no prey, no pay.” Their paycheques, in other words, are contingent on the successful capture and ransoming of a suitable vessel. This commission structure was clearly employed by Computer’s group; without the
Victoria
, the gang members’ remuneration would have consisted of nothing more than a one-way pleasure cruise in the Gulf of Aden.
3. COST STRUCTURE
Start-up Costs
According to Hansen, the cost of financing a pirate operation ranges from $300 to as high as $30,000. At almost $50,000, Computer’s initial capital outlay was off Hansen’s scale. To blame for his extravagant bill were the dual heavy-duty outboard motors he outfitted to the back of his unusually large attack boat; at 350 horsepower, they were among the most powerful and expensive available.
Operating Expenses
Operating expenses for a typical pirate group, Hansen writes, might run “as low as $100 per day.” At an estimated $3,000 per day, Computer’s gang spent money at a rate several orders of magnitude higher. In their love of deficit spending, however, Computer’s gang was typical. Hansen writes that a hijacked ship is often maintained on credit, and there is no doubt that this was the case with Computer’s operation.
4. ATTACK STRATEGY
Number of Attack Craft
The most common pirate attack strategy, Hansen argues, involves two skiffs (each typically holding five or six pirates), with one covering the other as its occupants attempt to scale the target vessel. Deploying one turbo-charged attack craft carrying nine hijackers, Computer’s modus operandi was atypical. Putting all your pirates in one boat has its perils; if, for instance, the
Victoria
crew had put up any resistance—such as blasting the would-be boarders with deck hoses—the absence of cover fire might have proved problematic. However, such a strategy also had several advantages: a more comfortable standard of living, additional room to store food and fuel, and more convincing fisherman camouflage.
Solitary Boarder
According to Hansen, standard operating procedure for a pirate boarding dictates that one lone man scale the sides of the target vessel before all others; in the words of Bossaso-based pirate “Red Beard”: “One man goes first and that man gives information back to us and we all board the ship then.” In this respect, the
Victoria
gang followed the industry norm; their trailblazer, of course, was Mohamed Abdi.
“Attack” and “Hold” Teams
“The groups are often, but not always, divided into an attack team and hold team,” writes Hansen. This attacker/holder dichotomy was certainly an organizational feature of Computer’s group. The attackers, like an entitled officer corps, enjoyed a higher status than the holders, and greater flexibility when it came to taking shore leave. Furthermore, the “three leaders” identified by hostage Traian Mihai all came from the attacker caste, and each attacker received a significantly higher payout than the holders.
5. TECHNOLOGY
Though Computer’s psychic directions undoubtedly gave the
Victoria
hijackers a unique advantage over other pirate groups, a sceptic might wonder if they had any additional help from modern technology. Hansen notes that pirates often possess such gadgets as night vision goggles, satellite telecommunications systems, and occasionally automatic identification systems that allow them to read the transponders of passing vessels. Added to this list should be basic marine navigation devices, such as GPS and radar systems.
There is no evidence to suggest that the
Victoria
hijackers possessed any of these accoutrements. The
Victoria
was carrying a cargo of rice, and was not the kind of glamorous prize about which a pirate would brag to his friends at the local khat
suq
. (Romanian media sources went so far as to report that the pirates may have mistaken the
Victoria
for an oil transport.
2
) Regardless, Computer’s group would probably not have targeted the
Victoria
if they had been able to read transponders or had detailed intelligence on vessel itineraries. Indeed, given the pirates’ utter lack of understanding of the
Victoria
’s radar display (as humorously recounted by Mihai), their attack craft almost certainly did not possess a marine radar system.
The more likely scenario is that the
Victoria
found
them
. With limited range and navigational technologies, the pirates were content to float in the IRTC and await a target of opportunity, like patient fishermen waiting for a nibble. In some respects, Levenescu may have been correct when he scornfully claimed that the IRTC had made the pirates’ job easier: though they faced a higher risk of death or capture, the transit corridor saved them the trouble of deciding where to hunt.
Another hypothetical indicator of a sophisticated pirate gang is the practice of gathering intelligence (cargo, itineraries, insurance details) on potential targets, either through “spotters”—informants located in major ports—or through membership in an online maritime tracking service, such as Lloyd’s Marine Intelligence Unit. For the same rationale as discussed above, there is little reason to think the
Victoria
hijackers made use of either of these resources.
In all probability, their most sophisticated technology was their own eyes, which would have proved quite capable of detecting the
Victoria
—and her telltale deck cranes—at a distance of ten kilometres.
6. ROLE OF THE DIASPORA
There has been much discussion in the media regarding the supposed transnational criminal networks controlling Somali pirate gangs from behind the scenes. As with many such myths, the drive for a good story often overwhelms the facts.
Though the existence of a transnational criminal conspiracy is highly overstated, the true level of the Somali diaspora’s involvement in piracy is less certain, and Hansen’s research does not help resolve the ambiguity. One of his pirate interviewees claimed that Somali expats from Kenya, Ethiopia, and the Gulf states sometimes provide technology such as goggles and telecommunications systems, as well as their translation services, but only rarely contribute money.
Like the clan networks within the country, the Somali diaspora is extremely integrated and close-knit, with Somali expats constantly moving in and out of Somalia even as they carry on normal lives in their adoptive homelands. The support provided by the diaspora—remittances, access to markets, business connections, and professional advice—is absolutely essential to making life inside Somalia liveable. “Pirate entrepreneurs” will seek to access these resources in the same way as legitimate local businessmen, but this is no more transnational crime than the foreign brother of a US citizen helping him to cheat on his income taxes.
The only known affiliation the
Victoria
gang had to the diaspora was through Loyan, their interpreter (Mihai told us that Loyan had studied in India for at least five years, which meant he must have held foreign citizenship, as it is virtually impossible to travel on a Somali passport). Men such as Loyan—English-speaking opportunists taking extended vacations in their homeland—are the real face of the so-called transnational criminal empire of Somali piracy.
7. OTHER
The Yemen Connection
Pirate attacks on Yemeni fishing ships, which are then converted for use as pirate motherships, have been well documented, and there are some indications that the
Victoria
gang may have been guilty of a double hijacking, the first involving a Yemeni vessel.