The Code Book (5 page)

Had the Arabs merely been familiar with the use of the monoalphabetic substitution cipher, they would not warrant a significant mention in any history of cryptography. However, in addition to employing ciphers, the Arab scholars were also capable of destroying ciphers. They in fact invented
cryptanalysis
, the science of unscrambling a message without knowledge of the key. While the cryptographer develops new methods of secret writing, it is the cryptanalyst who struggles to find weaknesses in these methods in order to break into secret messages. Arabian cryptanalysts succeeded in finding a method for breaking the monoalphabetic substitution cipher, a cipher that had remained invulnerable for several centuries.
Cryptanalysis could not be invented until a civilization had reached a sufficiently sophisticated level of scholarship in several disciplines, including mathematics, statistics and linguistics. The Muslim civilization provided an ideal cradle for cryptanalysis, because Islam demands justice in all spheres of human activity, and achieving this requires knowledge, or
ilm
. Every Muslim is obliged to pursue knowledge in all its forms, and the economic success of the Abbasid caliphate meant that scholars had the time, money and materials required to fulfill their duty. They endeavored to acquire the knowledge of previous civilizations by obtaining Egyptian, Babylonian, Indian, Chinese, Farsi, Syriac, Armenian, Hebrew and Roman texts and translating them into Arabic. In 815, the Caliph al-Ma’mūn established in Baghdad the Bait al-Hikmah (“House of Wisdom”), a library and center for translation.
At the same time as acquiring knowledge, the Islamic civilization was able to disperse it, because it had procured the art of papermaking from the Chinese. The manufacture of paper gave rise to the profession of
warraqīn
, or “those who handle paper,” human photocopying machines who copied manuscripts and supplied the burgeoning publishing industry. At its peak, tens of thousands of books were published every year, and in just one suburb of Baghdad there were over a hundred bookshops. As well as such classics as
Tales from the Thousand and One Nights
, these bookshops also sold textbooks on every imaginable subject, and helped to support the most literate and learned society in the world.
In addition to a greater understanding of secular subjects, the invention of cryptanalysis also depended on the growth of religious scholarship. Major theological schools were established in Basra, Kufa and Baghdad, where theologians scrutinized the revelations of Muhammad as contained in the Koran. The theologians were interested in establishing the chronology of the revelations, which they did by counting the frequencies of words contained in each revelation. The theory was that certain words had evolved relatively recently, and hence if a revelation contained a high number of these newer words, this would indicate that it came later in the chronology. Theologians also studied the
Hadīth
, which consists of the Prophet’s daily utterances. They tried to demonstrate that each statement was indeed attributable to Muhammad. This was done by studying the etymology of words and the structure of sentences, to test whether particular texts were consistent with the linguistic patterns of the Prophet.
Significantly, the religious scholars did not stop their scrutiny at the level of words. They also analyzed individual letters, and in particular they discovered that some letters are more common than others. The letters a and l are the most common in Arabic, partly because of the definite article al-, whereas the letter j appears only a tenth as frequently. This apparently innocuous observation would lead to the first great breakthrough in cryptanalysis.
Although it is not known who first realized that the variation in the frequencies of letters could be exploited in order to break ciphers, the earliest known description of the technique is by the ninth-century scientist Abū Yūsūf Ya’qūb ibn Is-hāq ibn as-Sabbāh ibn ‘omrān ibn Ismaīl al-Kindī. Known as “the philosopher of the Arabs,” al-Kindī was the author of 290 books on medicine, astronomy, mathematics, linguistics and music. His greatest treatise, which was rediscovered only in 1987 in the Sulaimaniyyah Ottoman Archive in Istanbul, is entitled
A Manuscript on Deciphering Cryptographic Messages;
the first page is shown in
Figure 6
. Although it contains detailed discussions on statistics, Arabic phonetics and Arabic syntax, al-Kindī’s revolutionary system of cryptanalysis is encapsulated in two short paragraphs:
One way to solve an encrypted message, if we know its language, is to find a different plaintext of the same language long enough to fill one sheet or so, and then we count the occurrences of each letter. We call the most frequently occurring letter the “first,” the next most occurring letter the “second,” the following most occurring letter the “third,” and so on, until we account for all the different letters in the plaintext sample.
Then we look at the ciphertext we want to solve and we also classify its symbols. We find the most occurring symbol and change it to the form of the “first” letter of the plaintext sample, the next most common symbol is changed to the form of the “second” letter, and the following most common symbol is changed to the form of the “third” letter, and so on, until we account for all symbols of the cryptogram we want to solve.
Al-Kindī’s explanation is easier to explain in terms of the English alphabet. First of all, it is necessary to study a lengthy piece of normal English text, perhaps several, in order to establish the frequency of each letter of the alphabet. In English, e is the most common letter, followed by t, then a, and so on, as given in
Table 1
. Next, examine the ciphertext in question, and work out the frequency of each letter. If the most common letter in the ciphertext is, for example, J then it would seem likely that this is a substitute for e. And if the second most common letter in the ciphertext is P, then this is probably a substitute for t, and so on. Al-Kindī’s technique, known as
frequency analysis
, shows that it is unnecessary to check each of the billions of potential keys. Instead, it is possible to reveal the contents of a scrambled message simply by analyzing the frequency of the characters in the ciphertext.
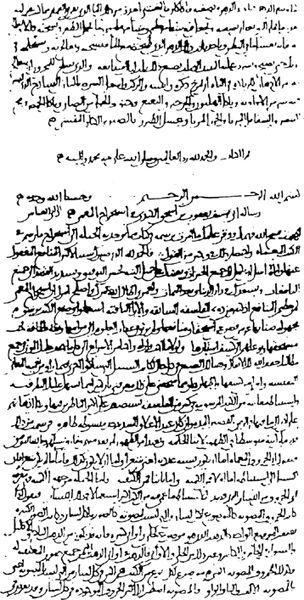
Figure 6
The first page of al-Kindī’s manuscript
On Deciphering Cryptographic Messages
, containing the oldest known description of cryptanalysis by frequency analysis. (
photo credit 1.2
)
However, it is not possible to apply al-Kindī’s recipe for cryptanalysis unconditionally, because the standard list of frequencies in
Table 1
is only an average, and it will not correspond exactly to the frequencies of every text. For example, a brief message discussing the effect of the atmosphere on the movement of striped quadrupeds in Africa would not yield to straightforward frequency analysis: “From Zanzibar to Zambia and Zaire, ozone zones make zebras run zany zigzags.” In general, short texts are likely to deviate significantly from the standard frequencies, and if there are less than a hundred letters, then decipherment will be very difficult. On the other hand, longer texts are more likely to follow the standard frequencies, although this is not always the case. In 1969, the French author Georges Perec wrote
La Disparition
, a 200-page novel that did not use words that contain the letter e. Doubly remarkable is the fact that the English novelist and critic Gilbert Adair succeeded in translating
La Disparition
into English, while still following Perec’s shunning of the letter e. Entitled
A Void
, Adair’s translation is surprisingly readable (see
Appendix A
). If the entire book were encrypted via a monoalphabetic substitution cipher, then a naive attempt to decipher it might be stymied by the complete lack of the most frequently occurring letter in the English alphabet.
Table 1
This table of relative frequencies is based on passages taken from newspapers and novels, and the total sample was 100,362 alphabetic characters. The table was compiled by H. Beker and F. Piper, and originally published in
Cipher Systems: The Protection Of Communication
.
| Letter | Percentage |
| a | 8.2 |
| b | 1.5 |
| c | 2.8 |
| d | 4.3 |
| e | 12.7 |
| f | 2.2 |
| g | 2.0 |
| h | 6.1 |
| i | 7.0 |
| j | 0.2 |
| k | 0.8 |
| l | 4.0 |
| m | 2.4 |
| n | 6.7 |
| o | 7.5 |
| p | 1.9 |
| q | 0.1 |
| r | 6.0 |
| s | 6.3 |
| t | 9.1 |
| u | 2.8 |
| v | 1.0 |
| w | 2.4 |
| x | 0.2 |
| y | 2.0 |
| z | 0.1 |
Having described the first tool of cryptanalysis, I shall continue by giving an example of how frequency analysis is used to decipher a ciphertext. I have avoided peppering the whole book with examples of cryptanalysis, but with frequency analysis I make an exception. This is partly because frequency analysis is not as difficult as it sounds, and partly because it is the primary cryptanalytic tool. Furthermore, the example that follows provides insight into the modus operandi of the cryptanalyst. Although frequency analysis requires logical thinking, you will see that it also demands guile, intuition, flexibility and guesswork.
Cryptanalyzing a Ciphertext
PCQ VMJYPD LBYK LYSO KBXBJXWXV BXV ZCJPO EYPD KBXBJYUXJ LBJOO KCPK. CP LBO LBCMKXPV XPV IYJKL PYDBL, QBOP KBO BXV OPVOV LBO LXRO CI SX’XJMI, KBO JCKO XPV EYKKOV LBO DJCMPV ZOICJO BYS, KXUYPD: “DJOXL EYPD, ICJ X LBCMKXPV XPV CPO PYDBLK Y BXNO ZOOP JOACMPLYPD LC UCM LBO IXZROK CI FXKL XDOK XPV LBO RODOPVK CI XPAYOPL EYPDK. SXU Y SXEO KC ZCRV XK LC AJXNO X IXNCMJ CI UCMJ SXGOKLU?”
OFYRCDMO, LXROK IJCS LBO LBCMKXPV XPV CPO PYDBLK
Imagine that we have intercepted this scrambled message. The challenge is to decipher it. We know that the text is in English, and that it has been scrambled according to a monoalphabetic substitution cipher, but we have no idea of the key. Searching all possible keys is impractical, so we must apply frequency analysis. What follows is a step-by-step guide to cryptanalyzing the ciphertext, but if you feel confident then you might prefer to ignore this and attempt your own independent cryptanalysis.
The immediate reaction of any cryptanalyst upon seeing such a ciphertext is to analyze the frequency of all the letters, which results in
Table 2
. Not surprisingly, the letters vary in their frequency. The question is, can we identify what any of them represent, based on their frequencies? The ciphertext is relatively short, so we cannot slavishly apply frequency analysis. It would be naive to assume that the commonest letter in the ciphertext, O, represents the commonest letter in English, e, or that the eighth most frequent letter in the ciphertext, Y, represents the eighth most frequent letter in English, h. An unquestioning application of frequency analysis would lead to gibberish. For example, the first word PCQ would be deciphered as aov.
However, we can begin by focusing attention on the only three letters that appear more than thirty times in the ciphertext, namely O, X and P. It is fairly safe to assume that the commonest letters in the ciphertext probably represent the commonest letters in the English alphabet, but not necessarily in the right order. In other words, we cannot be sure that O = e, X = t, and P = a, but we can make the tentative assumption that:
O = e, t or a, X = e, t or a, P = e, t or a.
Table 2
Frequency analysis of enciphered message.
| Letter | Frequency | |
| | Occurrences | Percentage |
| A | 3 | 0.9 |
| B | 25 | 7.4 |
| C | 27 | 8.0 |
| D | 14 | 4.1 |
| E | 5 | 1.5 |
| F | 2 | 0.6 |
| G | 1 | 0.3 |
| H | 0 | 0.0 |
| I | 11 | 3.3 |
| J | 18 | 5.3 |
| K | 26 | 7.7 |
| L | 25 | 7.4 |
| M | 11 | 3.3 |
| N | 3 | 0.9 |
| O | 38 | 11.2 |
| P | 31 | 9.2 |
| Q | 2 | 0.6 |
| R | 6 | 1.8 |
| S | 7 | 2.1 |
| T | 0 | 0.0 |
| U | 6 | 1.8 |
| V | 18 | 5.3 |
| W | 1 | 0.3 |
| X | 34 | 10.1 |
| Y | 19 | 5.6 |
| Z | 5 | 1.5 |